 |

Currently, we are collecting daily-traces from the following sampling points.
Traces are sampled at a fixed time of day. This is obviously not desirable and we need to find a better sampling method.
We started daily data collection at the trans-pacific point in February 1999. Since WIDE has a number of connections to the Internet exchange points, the return path of a session does not necessarily go through the same link.
The maximum size of each trace file is limited to about 100M bytes (about 40MB when compressed). We believe 100MB is an appropriate size for handling on a commodity PC as well as for fetching over the network, still it has enough information for statistical analysis.
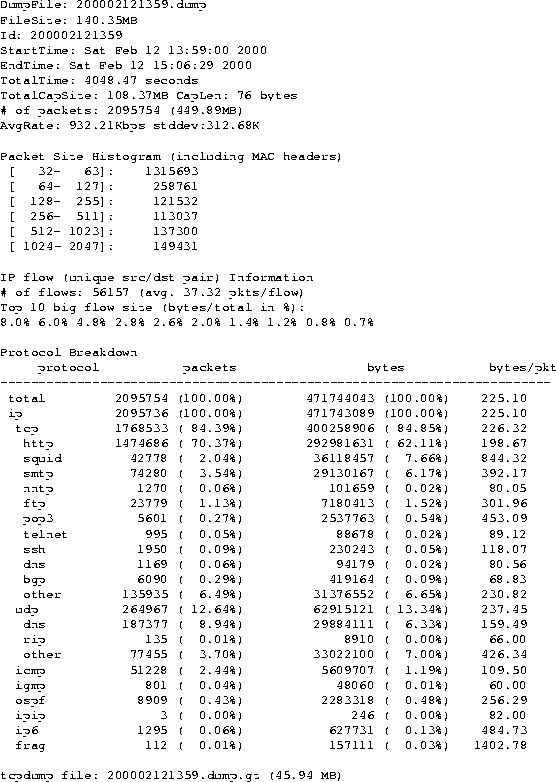
Figure 2 is a sample output of tcpdstat from the trans-pacific point on February 12, 2000. This 1-hour-long trace contains about 2 million packets, the number of unique address pairs is about 56K. HTTP is dominant in the trace, 70% of the total packets and 62% of the total bytes.
Among the collected traces, some data sets contain traces of DoS attacks such as portscan and smurf. These traces could be useful for developing tools to detect such attacks.
The 6bone point has been added in January 2000. The traffic volume of the 6bone point is still low; the average rate is around 100Kbps and the majority of traffic is BGP and ICMPv6. However, we expect IPv6 traffic will increase in a few years as major router and OS vendors have started shipping IPv6 support in their base systems. Our intention is to record the evolution of IPv6 traffic in a long term.
Figure 3 is the output of tcpdstat from the 6Bone point on the same day. This 3.5-hour long trace contains about 200K packets, the number of unique address pairs is about 270.
We expect that IPv6 traces will be useful for developing tools to support IPv6 since IPv6 traffic traces, especially on a backbone link, are not widely available.
Although we started collecting traces and made them available, we have not studied the traces thoroughly. Rather, one of the purposes of our open traffic repository is to leave analysis to those who are interested in doing it.
If other organizations start building similar but possibly closed traffic repositories, it would be possible to share experiences and development of tools. Especially, there are demands to develop a counter measure against the ever-growing threat of DoS attacks.