 |

lrk5, a popular Linux
rootkit. We start with a perfectly good target system and take
measurements of this system. Then, we launch a rootkit attack against
the target system and take measurements again after the attack.
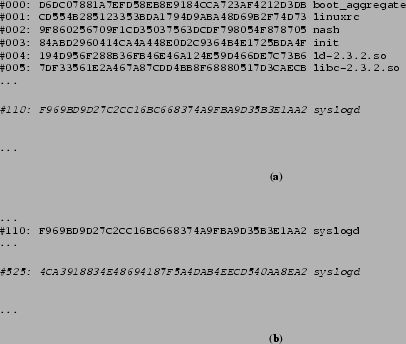
Figure 4(a) shows a (partial) list of
measurements for the good system, and
Figure 4(b) shows the corresponding list
of the same system that is compromised by a rootkit. The italicized
entries show that after the attack, the signature of the
syslogd program is different, indicating that the rootkit had
replaced the original syslogd with a Trojan version. This
example illustrates how such attacks can be discovered reliably using
our system.