
| Thomas Ristenpart * | Gabriel Maganis† | Arvind Krishnamurthy† | Tadayoshi Kohno† |
| *University of California, San Diego | †University of Washington |
| tristenp@cs.ucsd.edu | {gym,arvind,yoshi}@cs.washington.edu |
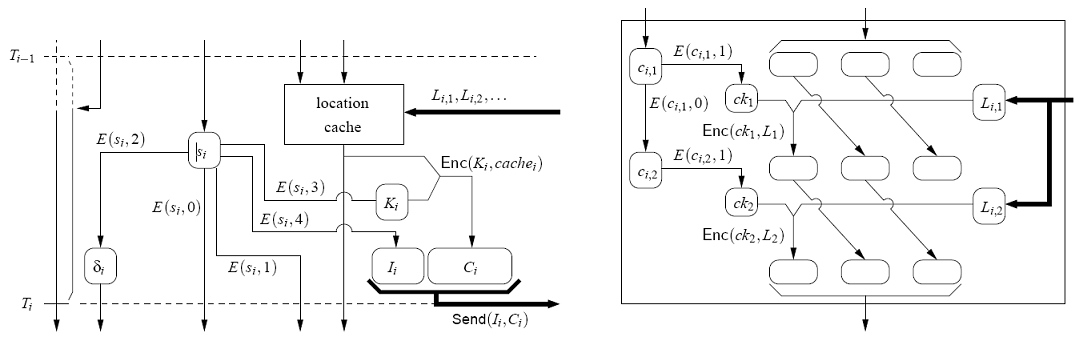
| Min | Mean | Median | Max | T/O | |
| Put | 207 | 1 021 | 470 | 11 463 | 2 |
| Get | 2 | 240 | 77 | 11 238 | 3 |
| Loc medium | 5 642 | 13 270 | 15 531 | 30 381 | - |
| Loc full | 17 446 | 36 802 | 36 197 | 63 916 | - |
| adeona-0.2.1 | r = 0 | r = 10 | r = 100 |
| Owner state | 75 | 75 | 75 |
| Client state (light) | 75 | 876 | 8 076 |
| Update (light) | 36 | 400 | 4000 |
| Client state (medium) | 75 | 27 116 | 270 476 |
| Update (medium) | 1 348 | 13 520 | 135 200 |
| adeona-0.1 | r = 0 | r = 10 | r = 100 |
| Owner state | 3 544 | 3 545 | 3 548 |
| Client state (full) | 1 779 | 30 824 | 292 184 |
| Update (full) | 1 452 | 14 520 | 145 200 |
| CPU | Wall | |||||||||
| Operation | Min | Mean | Median | Max | Min | Mean | Median | Max | T/O | |
| Initialize core | 210 | 329 | 330 | 460 | 215 | 367 | 348 | 1 082 | - | |
| Verify FSPRG state | 340 | 456 | 470 | 610 | 351 | 494 | 474 | 1 240 | - | |
| Panic encryption | 90 | 95 | 90 | 110 | 93 | 101 | 95 | 207 | - | |
| Panic decryption | 80 | 90 | 90 | 100 | 85 | 104 | 90 | 934 | - | |
| Panic update | r=0 | 440 | 559 | 570 | 700 | 612 | 1 653 | 977 | 15 347 | 9 |
| r=10 | 440 | 543 | 545 | 680 | 818 | 2 289 | 1 311 | 20 582 | 10 | |
| r=100 | 540 | 666 | 690 | 800 | 2 953 | 12 599 | 7 439 | 165 950 | 5 | |
| Panic retrieve | r=0 | 80 | 89 | 90 | 100 | 92 | 499 | 207 | 12 003 | 7 |
| r=10 | 80 | 87 | 90 | 100 | 93 | 705 | 335 | 9 734 | 12 | |
| r=100 | 80 | 87 | 90 | 100 | 116 | 2 458 | 1 555 | 21 734 | 5 | |